Today, hackers are not just very experienced computer users but they’re also really good psychologists. In order to avoid being deceived, you should know what information can be shared and what information must be kept secret.
5. Make up cognitive passwords

Many people use the same password for completely different resources, both corporate and personal. Some people think that it’s safe to replace a few symbols but keep the base of the password as is. This is not safe at all. Cybercriminals use password dictionaries which help them make a hack.
If you are scared of forgetting all your passwords because there are a lot of them, you can use a password manager or make up your own algorithm or memorization. It’s better to use “cognitive” passwords. Not a date of birth or for example, or the name of your favorite character; but instead use an association. For instance, use the first letters of your favorite poem combined with other symbols. It’s very unlikely that a hacker can find such a password in their dictionary.
4. Don’t cover your webcam
According to safety specialists, there is no point in covering your webcam. Even though it’s possible to watch someone through a webcam, in most cases, cybercriminals don’t use this method. What can they possibly see? Watching hours of video is hard and expensive.
Theoretically, smart televisions can be a bigger threat than webcams. But again, such surveillance is very rare. And besides, there are easier ways to steal data than this. We’ll tell you about these later in this article.
3. Remember the threat over your shoulder

Criminals often use an old-school method: they peek over our shoulders and look at the data that we enter in public places. To avoid such a threat, you can use special screens to make sure other people don’t see anything on your device. And of course, you should be especially careful when entering your access data for any account.
2. Use the 3-2-1 rule Advertising
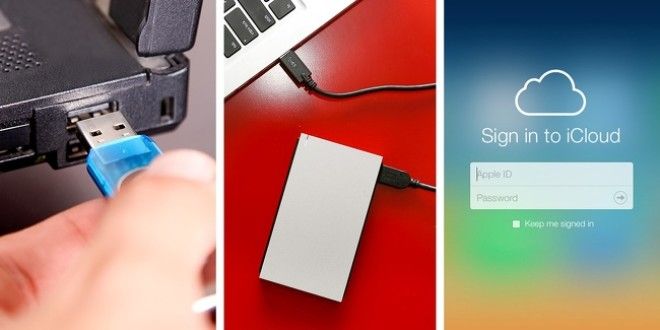
To avoid losing valuable information because of a cyber attack, use the rule 3-2-1. Data backup can be very valuable. If a hacker gains access to your computer, at least you will have the data on other storages. The rule is this:
- You have at least 3 copies (original and two copies).
- You use a different kind of storage (hard drive and cloud service).
- At least one copy is stored in a different place (for example, a safe).
1. Be attentive to addresses
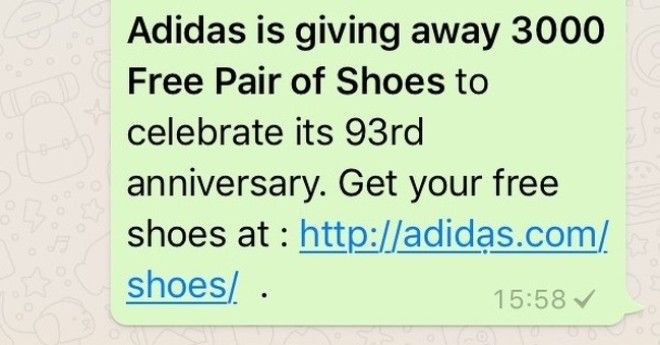
If you look at the screenshot closely, you will see how important it is to pay attention to detail. The address seems perfectly normal but if you look closer, you can see a dot under the second letter “a”. If you don’t notice it, you’ll go through the link which leads you to a dangerous website or sends a virus to your smartphone, tablet, or computer.
This situation can happen to people who think that they can type without looking at the keyboard. This often happens on virtual keyboards when fingers touch the nearest letters. Hackers know about this and create special programs which can create a list of possible typos and make false websites.
Two simple recommendations on how to avoid it:
- Look at the search field or the link that you got.
- Use special instruments that the browser has to avoid harmful resources.

